Arthur Besse
cultural reviewer and dabbler in stylistic premonitions
- 107 Posts
- 402 Comments
I think it depends which side of the debate one is on?
$ systemd-analyze calendar tomorrow Failed to parse calendar specification 'tomorrow': Invalid argument Hint: this expression is a valid timestamp. Use 'systemd-analyze timestamp "tomorrow"' instead? $ systemd-analyze timestamp tuesday Failed to parse "tuesday": Invalid argument Hint: this expression is a valid calendar specification. Use 'systemd-analyze calendar "tuesday"' instead?ಠ_ಠ
$ for day in Mon Tue Wed Thu Fri Sat Sun; do TZ=UTC systemd-analyze calendar "$day 02-29"|tail -2; done Next elapse: Mon 2044-02-29 00:00:00 UTC From now: 19 years 4 months left Next elapse: Tue 2028-02-29 00:00:00 UTC From now: 3 years 4 months left Next elapse: Wed 2040-02-29 00:00:00 UTC From now: 15 years 4 months left Next elapse: Thu 2052-02-29 00:00:00 UTC From now: 27 years 4 months left Next elapse: Fri 2036-02-29 00:00:00 UTC From now: 11 years 4 months left Next elapse: Sat 2048-02-29 00:00:00 UTC From now: 23 years 4 months left Next elapse: Sun 2032-02-29 00:00:00 UTC From now: 7 years 4 months left
(It checks out.)
Surprisingly its calendar specification parser actually allows for 31 days in every month:
$ TZ=UTC systemd-analyze calendar '02-29' && echo OK || echo not OK Original form: 02-29 Normalized form: *-02-29 00:00:00 Next elapse: Tue 2028-02-29 00:00:00 UTC From now: 3 years 4 months left OK $ TZ=UTC systemd-analyze calendar '02-30' && echo OK || echo not OK Original form: 02-30 Normalized form: *-02-30 00:00:00 Next elapse: never OK $ TZ=UTC systemd-analyze calendar '02-31' && echo OK || echo not OK Original form: 02-31 Normalized form: *-02-31 00:00:00 Next elapse: never OK $ TZ=UTC systemd-analyze calendar '02-32' && echo OK || echo not OK Failed to parse calendar specification '02-32': Invalid argument not OK

 2·2 days ago
2·2 days agoFunny that blog calls it a “failed attempt at a backdoor” while neglecting to mention that the grsec post (which it does link to and acknowledges is the source of the story) had been updated months prior to explicitly refute that characterization:
5/22/2020 Update: This kind of update should not have been necessary, but due to irresponsible journalists and the nature of social media, it is important to make some things perfectly clear:
Nowhere did we claim this was anything more than a trivially exploitable vulnerability. It is not a backdoor or an attempted backdoor, the term does not appear elsewhere in this blog at all; any suggestion of the sort was fabricated by irresponsible journalists who did not contact us and do not speak for us.
There is no chance this code would have passed review and be merged. No one can push or force code upstream.
This code is not characteristic of the quality of other code contributed upstream by Huawei. Contrary to baseless assertions from some journalists, this is not Huawei’s first attempt at contributing to the kernel, in fact they’ve been a frequent contributor for some time.

 71·3 days ago
71·3 days agoWasn’t Huawei trying to put a Backdoor into linux?
as far as i know, that has not happened.
what makes you think it did?

 53·6 days ago
53·6 days agofremdscham++😬

 12·13 days ago
12·13 days agoThe headline should mention that they’re breaking 22-bit RSA, but then it would get a lot less clicks.
A different group of Chinese researchers set what I think is the current record when they factored a 48-bit number with a quantum computer two years ago: https://arxiv.org/abs/2212.12372
I guess the news here is that now they’ve reached 22 bits using the quantum annealing technique which works on D-Wave’s commercially-available quantum computers? That approach was previously able to factor an 18-bit number in 2018.
🥂 to the researchers, but 👎 to the clickbait headline writers. This is still nowhere near being a CRQC (cryptanalytically-relevant quantum computer).

 10·21 days ago
10·21 days agoAll two-letter TLDs are ccTLDs.
However, several of them are not in ISO 3166-1.

 2·24 days ago
2·24 days agoOr you could just… learn to use the modern internet that 60% of internet traffic uses? Not everyone has a dedicated IPv4 anymore, we are in the days of mobile networks and CGNAT. IPv4 exhaustion is here today.
Where are you getting 60%? Google’s IPv6 Adoption page has it under 50% still:
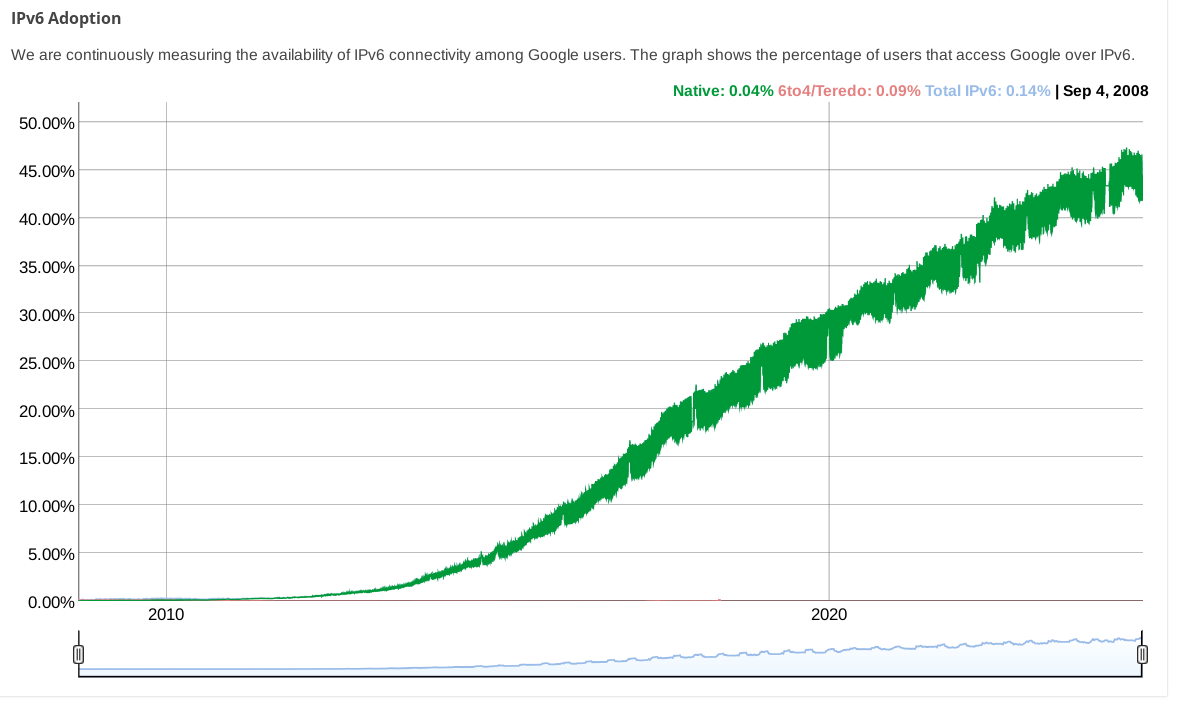
(while other stats pages from big CDNs show even less)

 1·24 days ago
1·24 days agoIf you have
::/0in your AllowedIPs and v6 connections are bypassing your VPN, that is strange.What does
ip route get 2a00:1450:400f:801::200e(an IPv6 address for google) say?I haven’t used wireguard with NetworkManager, but using
wg-quickit certainly adds a default v6 route when you have::/0inAllowedIPs.

 2·24 days ago
2·24 days agoYou could edit your configuration to change the wireguard connection’s
AllowedIPsfrom0.0.0.0/0to0.0.0.0/0,::/0so that IPv6 traffic is routed over it. Regardless of if your wireguard endpoint actually supports it, this will at least stop IPv6 traffic from leaking.

 3·24 days ago
3·24 days agoipv4 with an extra octet
that was proposed as “IPv4.1” on April 1, 2011: https://web.archive.org/web/20110404094446/http://packetlife.net/blog/2011/apr/1/alternative-ipv6-works/
In some places it is:


 183·26 days ago
183·26 days agowould this text land differently if “public school” were replaced with “school”? 🤔

 7·27 days ago
7·27 days agosee it’s conciser?

 211·27 days ago
211·27 days agoSo, they’re going to be “sovereign” over the whole archipelago, but only as long as they don’t exercise their sovereignty over the largest island in it which constitutes more than half of its total land area (30 km2 of 56.13 km2).
Today’s political agreement is subject to the finalisation of a treaty and supporting legal instruments, which both sides have committed to complete as quickly as possible. Under the terms of this treaty the United Kingdom will agree that Mauritius is sovereign over the Chagos Archipelago, including Diego Garcia. At the same time, both our countries are committed to the need, and will agree in the treaty, to ensure the long-term, secure and effective operation of the existing base on Diego Garcia which plays a vital role in regional and global security. For an initial period of 99 years, the United Kingdom will be authorised to exercise with respect to Diego Garcia the sovereign rights and authorities of Mauritius required to ensure the continued operation of the base well into the next century.
The treaty will address wrongs of the past and demonstrate the commitment of both parties to support the welfare of Chagossians. Mauritius will now be free to implement a programme of resettlement on the islands of the Chagos Archipelago, other than Diego Garcia, and the UK will capitalise a new trust fund, as well as separately provide other support, for the benefit of Chagossians.
It will also herald a new era of economic, security and environmental partnership between our two nations. To enable this partnership the UK will provide a package of financial support to Mauritius. This will include an indexed annual payment for the duration of the agreement and the establishment of a transformational infrastructure partnership, underpinned by UK grant funding, to deliver strategic projects generating meaningful change for ordinary Mauritians and boosting economic development across the country. More broadly, the UK and Mauritius will cooperate on environmental protection, maritime security, combating illegal fishing, irregular migration and drug and people trafficking within the Chagos Archipelago, with the shared objective of securing and protecting one of the world’s most important marine environments. This will include the establishment of a Mauritian Marine Protected Area.
Nice touch making a new “Marine Protected Area” in the process; the current “Chagos Marine Protected Area” was created entirely to, well… lets let this 2009 US diplomatic cable published by WikiLeaks explain:
1. (C/NF) Summary. HMG would like to establish a “marine park” or “reserve” providing comprehensive environmental protection to the reefs and waters of the British Indian Ocean Territory (BIOT), a senior Foreign and Commonwealth Office (FCO) official informed Polcouns on May 12. The official insisted that the establishment of a marine park – the world’s largest – would in no way impinge on USG use of the BIOT, including Diego Garcia, for military purposes. He agreed that the UK and U.S. should carefully negotiate the details of the marine reserve to assure that U.S. interests were safeguarded and the strategic value of BIOT was upheld. He said that the BIOT’s former inhabitants would find it difficult, if not impossible, to pursue their claim for resettlement on the islands if the entire Chagos Archipelago were a marine reserve. End Summary.
I wonder how the “treaty will address wrongs of the past”; somehow I doubt it will involve any mention of the CIA torture site there.














that flag is upside down 🤘